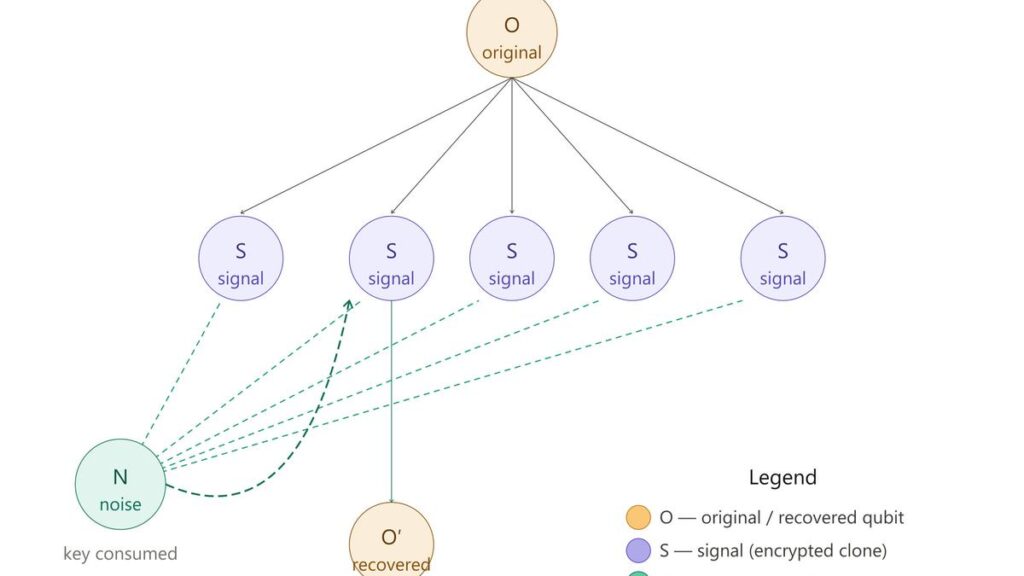
Researchers have shown a loophole in the no-cloning theorem by creating perfect copies using ideas from information theory. The protocol is illustrated here.
| Photo Credit: Image created with Sonnet 4.6
Quantum physics has a rule called the no-cloning theorem that prevents you from making a perfect copy of an unknown quantum state. It has shaped everything from quantum cryptography to quantum computing, and researchers have largely accepted it as an inalienable constraint.
Copying data in classical computing is trivial. We routinely copy files to the cloud for backup and make copies of code to share it. Quantum computers, however, cannot do any of this in the obvious way because of the no-cloning theorem, which is thus a serious obstacle to building robust quantum infrastructure.
But recently, a team of physicists from Japan, Canada, Germany, and IBM Quantum experimentally demonstrated a loophole in the theorem, showing that quantum information can indeed be duplicated provided the clones remain encrypted.
A key for noise
Previous researchers had developed approximate methods that produced imperfect copies with about 83% fidelity, the proven maximum for these approaches. But these copies were noisy and impractical.
In 2023, Koji Yamaguchi and Achim Kempf — two of the new paper’s authors — reported the loophole (published in Physical Review Letters on January 6 this year). Rather than accepting degraded copies, they proved (on paper) that it is possible to create perfect ones as long as each copy is scrambled by quantum noise so that it is individually useless.
This noise is not random. It is recorded in a set of ‘noise qubits’ that serves as the decryption key. To create clones, the original qubit is allowed to interact with a series of signal qubits, called the quantum register, in a way that spreads the information across multiple signal qubits. At this stage, each new qubit is a clone but also a maximally mixed state, meaning it looks like random noise to an observer.
When you want to recover the original state, you apply the decryption operation to any one of the encrypted clones using the full set of noise qubits. This restores the original perfectly. But the decryption process consumes the key. So after you decrypt one clone, the key is gone and every remaining clone becomes permanently scrambled. Which means you only get one perfect recovery. (The no-cloning theorem says you cannot freely access multiple identical copies.)
Four tests
To test this idea, the team ran experiments directly on the IBM Heron R2 superconducting processors, which feature 156 physical qubits, using up to 154 qubits across four experiments.
The first experiment measured how fidelity — how close the recovered state is to the original state — decayed as the number of encrypted clones grew from 2 to 15. The team found that making more copies did not make each copy harder to recover. The second test confirmed that the clones were quantum rather than classical.
The third was the most ambitious. Instead of creating all clones in a single step, the team cloned one qubit, then cloned those clones, and so on. Using all 154 available qubits, the researchers found that with more qubits with equal levels of noise, up to 729 clones could be produced while keeping the signal detectable.
Finally, the team applied the protocol in parallel across multiple qubits simultaneously entangled in a GHZ state — a complex form of entanglement involving many qubits. And they confirmed that they could use encrypted cloning to back up entire quantum registers rather than just single isolated qubits.

Refined understanding
According to the authors of the study, their experiments require scientists to refine the understanding of the no-cloning theorem. They argued that the real constraint is not that quantum information cannot be copied and spread widely — it can — but that the access to that information is restricted and that each setup allows only one shot at retrieving it.
“For example, encrypted cloning enables … redundant quantum cloud storage: a quantum cloud storage provider hosts encrypted clones of a client’s quantum data on separate servers,” the authors wrote. “As long as at least one of the servers survives, the client can recover all of their data perfectly by decrypting the surviving clones. Quantum cloud storage could serve as a platform also for quantum cloud computing.”
This is a rare instance in which a new, profound idea has been tested almost immediately, and the initial results prove that the protocol performs as expected. A key advantage of this protocol over many earlier proposals is that the recovered qubit is identical to the original state rather than an approximate copy. The work is sure to stimulate further research on building reliable quantum memories, which are essential for many quantum information processing protocols.
S. Srinivasan is a professor of physics at Krea University.
Published – April 03, 2026 07:30 am IST